As the Apache Log4j vulnerability is growing massively and its spread all over the internet a lot of worldwide companies are affected mostly on their Java-based applications. Elasticsearch among the others is highly affected by Log4j, the impact is still under high pressure as the number of affected companies is ramping up. We all must act quickly and follow the best practice to protect the well-known ELK stack.
Here I’m going to cover a few scenarios on how to protect the Elasticsearch stack from Apache Log4j depending on different hosting environments.
Prerequisites
- ELK stack
ELK stack on Linux
If your ELK stack is installed and running on a Linux server, first you need to check your Elasticsearch version.
curl -XGET 'http://elasticsearch-endpoint-url'
From the output, you need to find the version parameter.
To protect your ELK stack you’ll have to update the Elasticsearch version to 7.16.1. For more info please visit the official Elasticsearch guide.
ELK stack on Docker
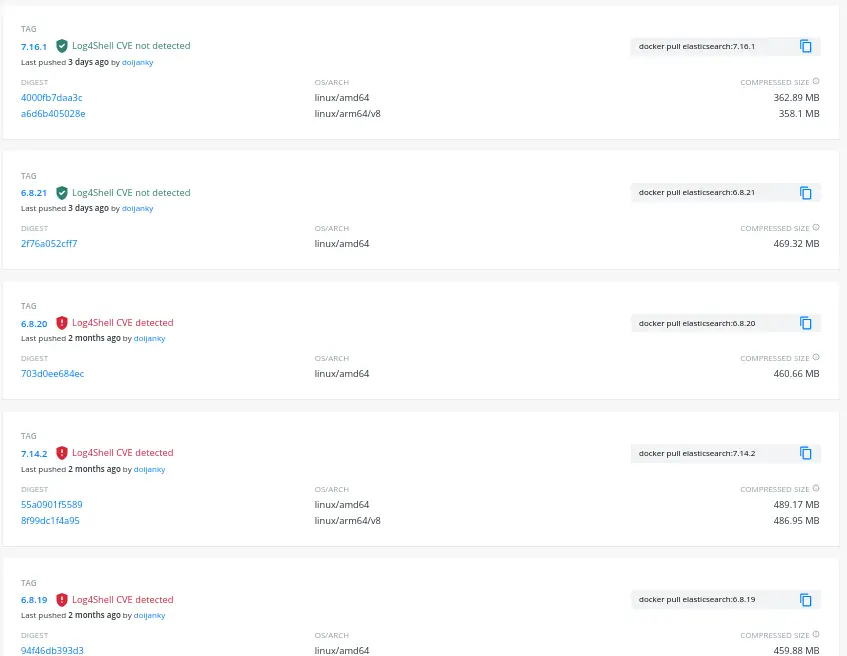
If your ELK stack is Dockerized and you are using the official Elasticsearch Docker image from the Docker hub repo, you should visit the Docker hub web page where you can clearly see which versions are safe and protected(7.16.1 and 6.8.21). Most of the image versions are already scanned and the safe ones to use are on the top of the list:
ELK stack on AWS
When it comes to AWS most of the Elasticsearch core operations and configuration files are managed by their side. They created a new Amazon OpenSearch Service which is successor to Elasticsearch service, and the best advice is to follow the AWS update Apache log4j2 page.
They have provided a list of services and how to mitigate the log4j impact but specifically, the advice for OpenSearch is:
Amazon OpenSearch Service has released a critical service software update, R20211203-P2, that contains an updated version of Log4j2 in all regions. We strongly recommend that customers update their OpenSearch clusters to this release as soon as possible.
Conclusion
If you have any additional concerns regarding Elasticsearch and how to keep it safety don’t hesitate to put a comment below. If you find this tutorial useful, follow our official channel on Telegram.